À Madagascar, une simple signature peut bloquer tout un projet.
Une demande d’autorisation qui attend sur un bureau, un courrier qui voyage d’un ministère à un autre, un dossier validé … à moitié.
Tout le monde le sait : la lenteur administrative n’est pas toujours une question de mauvaise volonté, mais souvent de procédures papier, signatures physiques et déplacements inutiles.
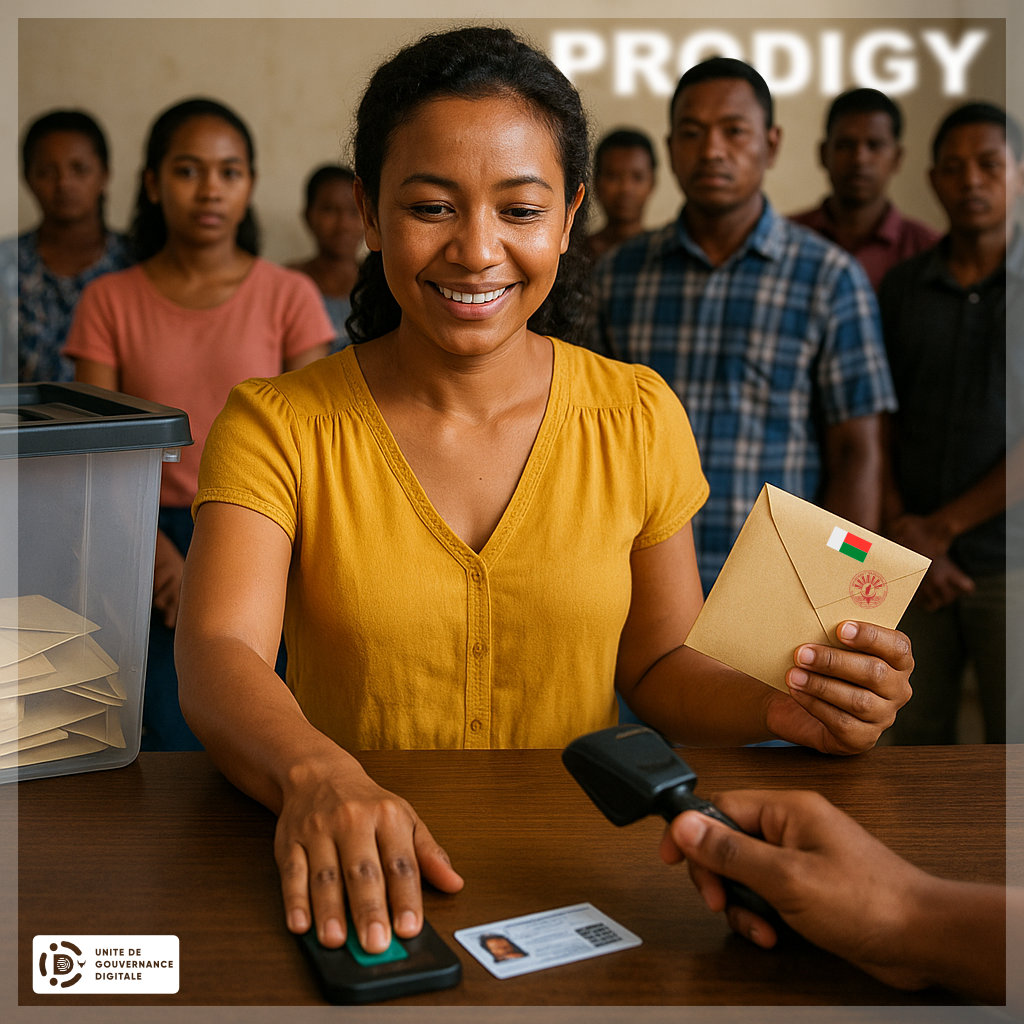
C’est là que PRODIGY apporte une véritable révolution silencieuse : l’identité numérique et la signature électronique.
1. Quand une signature ne dépend plus d’un stylo ni d’un tampon
Dans la plupart des administrations, signer un document signifie imprimer le formulaire en six exemplaires, completer au stylo chaque exemplaire, parapher chaque page, signer puis faire la queue pour deposer les documents dans le bureau compétent.
Chaque étape ajoute un risque d’erreur, de perte, ou tout simplement … de délai.
Avec la signature électronique, tout cela devient instantané : le responsable reçoit un document numérique, le vérifie, le signe depuis son poste ou son smartphone, et la signature est légalement équivalente à celle sur papier.
Et ce n’est pas de la théorie.
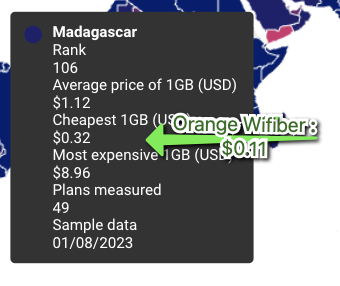
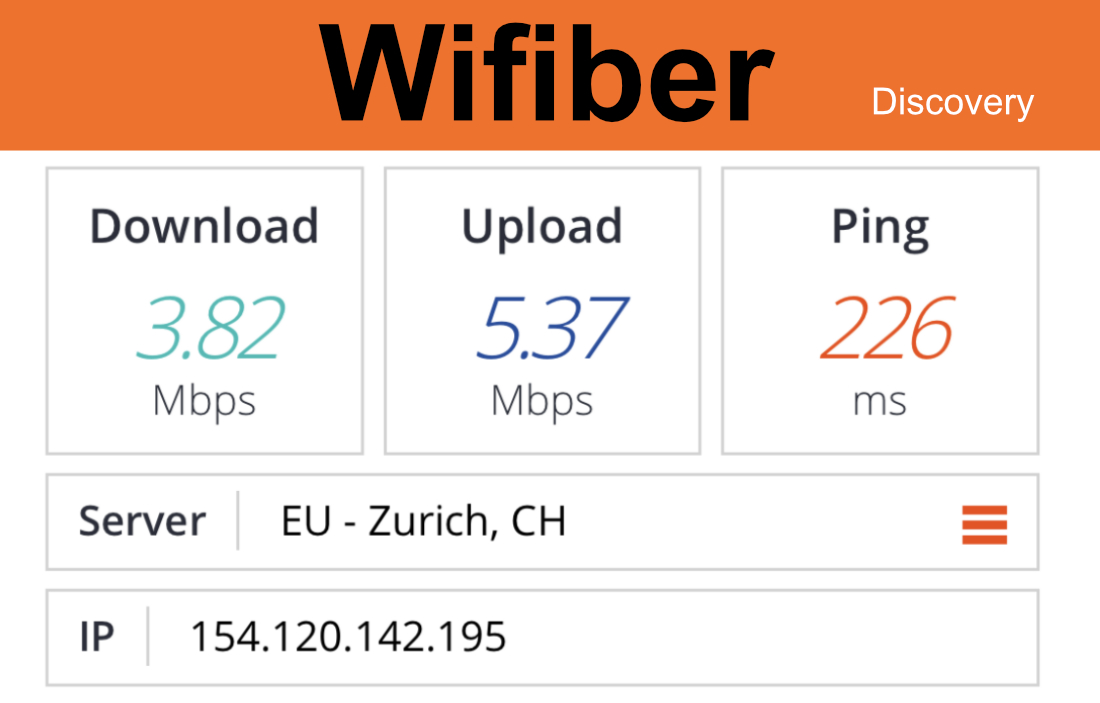
L’Unité de Gouvernance Digitale (UGD), financé par PRODIGY, construit justement la PKI nationale, cette infrastructure de confiance qui permet de prouver qui signe, quand, et avec quelle garantie d’intégrité.
Une fois que cette PKI sera accessible au grand public, une simple signature numérique suffira pour authentifier une décision publique, un contrat, un marché, une autorisation.
2. L’identité numérique, le cœur de la confiance
Mais pour qu’une signature électronique ait de la valeur, il faut savoir qui signe.
Et c’est là que la carte d’identité numérique de PRODIGY entre en scène.
Chaque citoyen et chaque agent public pourra être identifié de manière fiable, grâce à une carte ou un identifiant numérique adossé à des données biométriques.
Concrètement, cela veut dire que :
Le ministère saura que c’est bien le directeur qui a signé un document, pas son assistant. Une entreprise saura que le marché public est réellement validé par un fonctionnaire habilité. Un citoyen saura que la lettre officielle reçue par e-mail n’est pas un faux.
Cette double garantie (identité numérique + signature électronique) crée un écosystème de confiance inédit à Madagascar.
3. Une administration plus rapide, plus propre, plus transparente
Imaginez le parcours d’un dossier aujourd’hui : un fonctionnaire rédige une note, la fait parapher, l’envoie à la direction, qui l’imprime, la signe, la renvoie, puis la transmet au ministère suivant.
Résultat : des semaines d’attente, photocopies, cachets, enveloppes, perte de trace.
Avec PRODIGY, ce même processus peut se faire en une journée :
L’agent crée le document électronique, le responsable le signe avec son certificat numérique, Le système envoie automatiquement une trace infalsifiable (horodatage, identité, contenu).
Résultat : Moins de papier, Moins de déplacement, Moins de perte d’information, Et surtout, plus de traçabilité. Un audit devient simple : on sait qui a signé quoi et quand. La corruption devient plus difficile, parce que tout est enregistré.
4. Le secteur privé aussi y gagne
Ce n’est pas seulement l’administration qui y gagne.
Les entreprises malgaches, grandes ou petites, profiteront directement de cette infrastructure.
Signer un contrat de prestation, un devis, ou un bon de commande ?
Plus besoin d’imprimer, parapher et faire courir le document entre Tana, Toamasina et Mahajanga.
Une signature électronique qualifiée, adossée à la PKI nationale, aura valeur légale.
Les banques pourront valider des crédits sans déplacement, les assurances signer des contrats à distance, et les notaires certifier des actes électroniques sans piles de papier.
C’est du temps gagné, donc de la productivité.
Et surtout, cela ouvre la porte à de nouveaux services numériques malgaches : e-commerce sécurisé, télétravail légalement reconnu, création d’entreprise en ligne, etc.
5. Et pour le citoyen ?
C’est peut-être le plus important.
Aujourd’hui, pour obtenir un extrait de naissance, un casier judiciaire ou un certificat de résidence, il faut se déplacer, remplir des papiers, revenir chercher le document signé.
Demain, avec une identité numérique et la signature électronique, le citoyen pourra faire ses démarches depuis son téléphone.
- Il recevra son document signé numériquement, valide et vérifiable, sans avoir à se déplacer.
- Un jeune entrepreneur pourra créer sa société en une journée.
- Une mère de famille pourra renouveler les papiers de ses enfants sans perdre une journée de travail.
- Un étudiant pourra obtenir ses relevés certifiés sans aller frapper à quatre portes.
C’est cela, le vrai changement : rendre l’État accessible.
6. Moins de bureaucratie, plus de confiance
La signature électronique, ce n’est pas juste une modernisation technique. C’est un changement culturel.
Elle transforme la relation entre l’État, les citoyens et les entreprises : moins de files d’attente, moins de tampons, plus de transparence.
Et quand les procédures sont claires, rapides et traçables, la confiance revient.
Les citoyens croient à nouveau en leur administration.
Les investisseurs croient à nouveau au pays.
C’est précisément ce que vise PRODIGY : remettre la confiance au centre de l’action publique.
Conclusion
Madagascar n’a pas besoin d’une administration plus grosse.
Elle a besoin d’une administration plus intelligente.
Grâce à l’identité numérique et à la signature électronique, PRODIGY donne enfin à l’État les outils pour agir vite, bien et de manière fiable.
Ce n’est pas un gadget technologique.
C’est une révolution du quotidien : pour les fonctionnaires, les entreprises, et surtout pour les citoyens.